How Can We Help?
Search for answers or browse our knowledge base.
Create New Connector
Connectors share the same common settings, specific connector settings, behaviors and limitations can be found in the system connectors section
System Connector
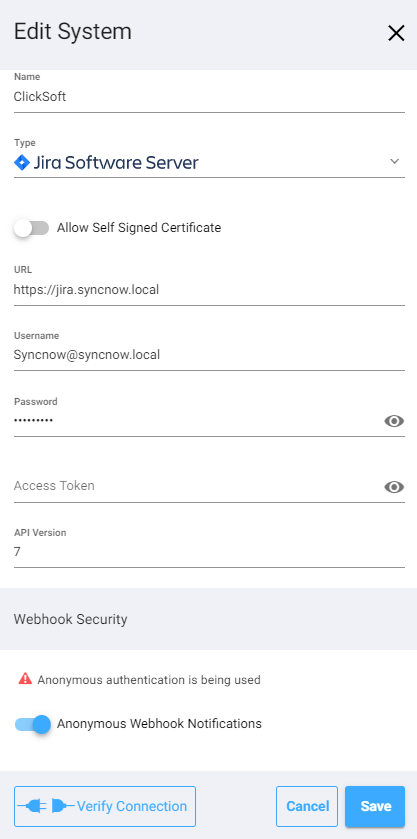
- Name – the name of the connector.
- Type – The system type of the connector
- Check Allow Self Signed certificate to allow connectivity to the connector even if is self signed
- URL – Add the base URL of the system
- Usernamepassword – set here the username that issued the token and the password.
- UsernameToken – Set this if the system if the system uses token for communication (recommended).
- API Version – API Versions is being used with several connector, please look at the system connectors section for information regarding specific connector.
Warning
It is not recommended to allow self signed certificates for production environment, check only for testing environments
Webhook Security
Webhooks are used for continuous synchronization, we register them for you when you activate a process.
- Anonymous notifications – use this if the source system (Azure DevOps | Jira | ServiceNow etc) supports only anonymous notifications to SyncNow. If Anonymous notifications is checked then SyncNow will not authenticate source requests to its notification API.We strongly recommend to Add IP restrictions if Anonymous notifications is checked.
- Allowed IP Addresses – check this to allow specific IP addresses or IP ranges in the format of network/mask separated with commas from which SyncNow will allow webhook notifications to its API.
Warning
If Anonymous notifications is checked then SyncNow will not authenticate source requests to its notification API.
We strongly recommend to add IP restrictions if Anonymous notifications is checked.
